When doing some network engineering, it’s sometimes necessary to tunnel across IP-clouds. There are multiple reasons why one would use a tunnel:
- Security: You don’t want the carrier-network to see your data
- IP conflicts and/or routing issues: You want to carry private IP addresses (eg 10.0.0.0/8 in IPv4) across a public segment (eg the Internet)
- Workarounds: for whatever reason you whised that there was a connection between A and B
Technically, a tunnel consists of taking a bunch of bytes and re-packaging it. The well knows GRE-tunnel takes IP packets and encapsulates them in another IP packet. The outer IP-layer is used to carry the packet across to the other endpoint, where the inner IP-layer reappears. Other tunnels operate at different layers. SSH for example encapsulates TCP segments inside its TCP-connection; SSL-based VPN encapsulate IP packets inside their TLS-session.
Especially in the third case, workarounds, it would be very practical to be able to build a layer 2 tunnel: transport raw ethernet frames, including IEEE802.1q VLAN tags. This is called the L2TP, Layer 2 tunneling protocol. The current version (3) is defined in RFC 3931.
The Cisco website has a complete page on L2TP, in all its variants (Frame relay over MPLS, HDLC over ATM, …). I only wanted to do ethernet over IP. This is the (partial) router configuration I used. Items in bold need to be adapted on the receiving end.
pseudowire-class PW_TEST encapsulation l2tpv3 protocol none ip local interface FastEthernet0/1 ! interface FastEthernet0/0 no ip address xconnect 10.0.0.3 1 encapsulation l2tpv3 manual pw-class PW_TEST l2tp id 2 3 ! interface FastEthernet0/1 ip address 10.0.0.2 255.255.255.
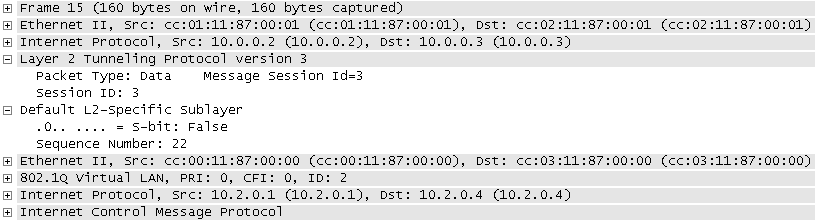
This is all that is needed to tunnel every frame of Fa0/0 to 10.0.0.3 (and back). I pinged through this tunnel using both the native VLAN and a tagged vlan. Here is the resulting PCAP file. Wireshark shows the tunneled ethernet frame:

confused says:
What is the WAN link and address in the example?
2009-08-18, 1:56What is the interface with subinterfaces and 802.1Q in the example?
thanks
Niobos says:
There is no specific WAN-interface or address. The above example will take every Ethernet frame it receives on Fa0/0 and encapsulate it in an IP packet, destined to 10.0.0.3. This IP packet will be processed just like every other IP packet.
In the example above, the packet is sent over a normal LAN via Fa0/1, but it could just as well be an IPsec VPN.
Since this whole procedure works on Ethernet frames, you don’t need to define any 802.1q parameters, nor subinterfaces. Every frame is encapsulated as-is, including a dot1Q header (if present).
Hope this clears things up a bit.
2009-08-18, 17:30Greg says:
Is it just as simple to configure this on a vlan or port channel? This L2TP documentation that Cisco has is gonna make my head explode!
2010-02-23, 22:08Greg says:
PS. Would you mind posting a copy of your entire config?
2010-02-23, 22:12Niobos says:
Hi Greg,
I haven’t tried it on a VLAN or port-channel, so I can’t answer that. Technically I don’t see a problem, but it might be unimplemented…
As for the entire configuration, I’d have to re-create it myself. The only thing you need beside the posted lines is working router (having IP connectivity to the other end). I’m sure you’ll find plenty of examples in pretty much every book/website on Cisco. If you really can’t figure it out, I’ll re-create the full config and post it.
2010-02-23, 22:45newbie says:
Can this technique be used to connect to switches over the internet ?
Can the two switches then exchange cdp / spanning tree bpdus etc ?
Also, is this only on very high end cisco platforms ?
2010-07-13, 16:48Niobos says:
Yes, this can be used to connect switches over the internet, but please consider the security-side as well.
2010-07-14, 16:20The two routers act like a single bridge. Technically it’s no problem to transport CDP or STP packets, but you need to take care that the routers don’t interpret the packet themselves before they’re transmitted. I haven’t tested this, and I’m not sure whether you want this.
L2TP is an IETF standard, so non-Cisco devices can implement it as well. Cisco’s feature navigator tells me that L2TP is available even on an Cisco 867, so definitely not “high end only”.
Ethernet says:
böyle güzel bilgiler için teşekürler…
2010-08-09, 10:55Brandon B says:
is there a limitation on speed? a friend and i want to setup eoip between our two 1000 base routers, there about a mile apart. we want to transfer files between our networks
2012-08-20, 16:30Niobos says:
There is no artificial limitation of speed. L2TP will go as fast as your devices can (de)encapsulate and your link can carry.
Do note, however, that protocols designed for LAN-use might suffer a lot when used over (relatively) slow internet-links. The usual example is Microsoft’s SMB/CIFS protocol.
Also, if you just want to transfer files, there is no need to set up L2TP, you can just use regular routing.
2012-08-20, 18:25VLAN over WAN - Just just easy answers says:
[…] take a look to : http://blog.dest-unreach.be/2009/05/05/ethernet-over-ip-l2tp-on-cisco http://www.cisco.com/en/US/docs/ios/12_0s/feature/guide/l2tpv325.html […]
2013-09-06, 12:05